AI-driven testing just got smarter. Discover SOAtest 2025.1. >>
Jump to Section
Iron Bank Your DevSecOps for Continuous Software Assurance
DevSecOps has created a new wave in software development across several organizations, making it an integral part of the CI/CD process. Learn how containerizing the Parasoft SAST solution benefits your organization’s software delivery.
Jump to Section
Jump to Section
DevSecOps has gained considerable momentum as a de facto process for formalizing and integrating security testing as part of continuous integration and continuous deployment/delivery (CI/CD) process. By integrating security into a CI/CD process, organizations can automate security testing that triggers each developer commit, avoiding delays as a gated process or tacking it on at the end.
CI/CD is the heartbeat of modern software development and organizations realize the need to instantiate a CI/CD pipeline to automate and streamline their software delivery process.
DoD Modernizing Software Development
The Department of Defense (DoD) realizes the shift in modern software development and is undergoing digital transformation to increase mission agility in supporting warfighters and field operations. Delivering software capabilities every three to ten years makes it impossible to keep up with the pace of technology. As a result, DoD has launched an Enterprise DevSecOps initiative to modernize and transform its approach to software delivery.
Launching Enterprise DevSecOps Initiative
This initiative is comprised of several components designed to enhance software security, improve infrastructure capabilities, streamline IT processes, and modernize compliance processes to enable DoD-wide continuous Authority to Operate.
As part of DoD’s Enterprise DevSecOps initiative, a central repository of authorized, hardened, and accredited containers of best-of-breed software development tools and capabilities were created. This central repository, known as Iron Bank, is designed to lower the bar in fielding DevSecOps solutions across DoD software programs.
Given the recent and increasing threats to compromise CI/CD toolchains and DevSecOps pipelines as seen with the SolarWinds breach, DoD is looking to leverage Iron Bank to accelerate the adoption of DevSecOps to secure the software delivery process for all DoD software programs.
The Iron Bank repository hosts both free and open source (FOSS) and commercial off-the-shelf (COTS) software development tools. Containers in Iron Bank are hardened based on the agency’s container hardening guide to allow DoD-wide reciprocity across classifications.
Parasoft SAST in Iron Bank
DoD software programs can power their CI/CD pipeline and toolchains with Parasoft C/C++test, the most complete static application security testing (SAST) solution for C and C++, that leverages comprehensive analysis techniques (pattern-based analysis, data flow analysis, and abstract interpretation) to expose critical vulnerabilities that often lead to cyberattacks.
Expose Critical Vulnerabilities With Parasoft C/C++test
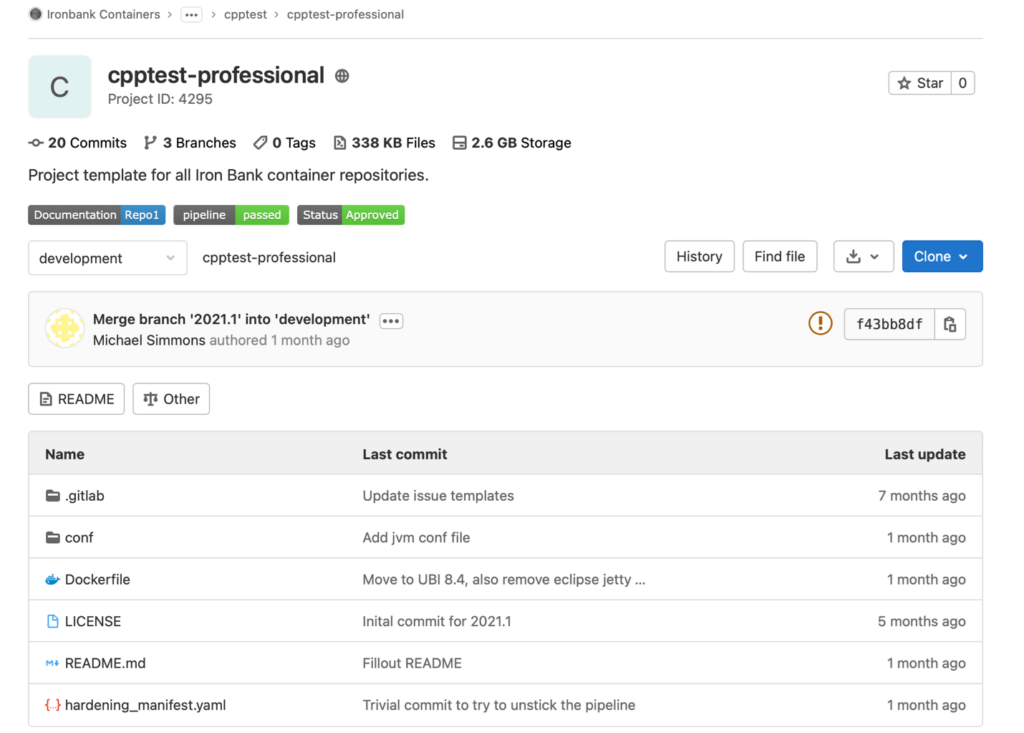
It’s currently hosted on Iron Bank’s GitHub as a dockerfile and is intended to be used as a base image for C/C++ compiler toolchains. Both the standard and professional versions are available to help DoD software programs formalize SAST and unit testing capabilities as part of their software testing. Parasoft recognizes that the ability to develop, deploy, and continuously improve software is essential to national defense.
Parasoft C/C++ test is ideal for embedded software development and can help enforce and validate security and quality compliance standards, such as Common Weakness Enumeration (CWE), CERT Secure Coding standards, MISRA and AUTOSAR to name a few, as well as compliance validation for DISA STIG and OWASP.
A Growing Embedded Market
Recent studies suggest that the military (national defense) embedded systems market size is projected to grow from 1.4 billion in 2020 to 2.1 billion by 2025 at a CAGR of 8.3% from 2020 to 2025.
Parasoft realizes this growing demand and has committed to investing significant resources to ensure our C/C++test SAST solution can be containerized to meet DoD hardening and security standards. This provides a unique opportunity for Parasoft to work with DoD software programs in meeting their mission objectives of digital transformation and modernizing software development practices to deliver assured software security at speed.
Iron Bank Your DevSecOps
Containerizing Parasoft SAST solution provides the following benefits to DoD software programs.
- Automates security testing in CI/CD pipeline for code changes submitted by developers to keep pace with software delivery cadence.
- Provides the ability to integrate security and compliance into DevOps tools and workflows to enforce security and compliance standards to help inform risk management decisions.
- Helps improve collaboration between developers and security teams with remediation workflow analysis, detailed reporting of findings, code coverage details, and reporting analytics to pinpoint what matters the most.
- Supports Continuous Authority to Operate (cATO) activities by providing real time visibility into risks and metrics identified through security testing. This can be used to extend reciprocity across DoD software programs to accelerate and inform cATO activities.
- Provides in-depth analysis feedback that integrates into developers’ workflow that guides developers in remediating vulnerabilities and improving coding practices.
These benefits are essential for helping DoD meet its mission needs and realize the limitless possibilities in modern software development. Formalizing software security testing early with a shift-left mindset is non-negotiable for critical systems and must build on continuous software assurance principles. Do it early and do it often.
Expose Critical Vulnerabilities With Parasoft C/C++test
“MISRA”, “MISRA C” and the triangle logo are registered trademarks of The MISRA Consortium Limited. ©The MISRA Consortium Limited, 2021. All rights reserved.
Related Post + Resources